My website was under attack! How I protected it.
Last week I launched a quick landing page with a waitlist.
I had a product idea, but I was not very convinced, so I tried to validate it.
A website is publicly available, and for the waitlist, I added an endpoint (public) to collect the emails of the people interested.
To collect potentially interested people, I launched the landing page on my usual channels, Twitter / X and Reddit, but after a couple of days, I noticed this 👇
18.000 events in a few seconds. I was clearly under attack.
It’s important to notice that these events could always happen, regardless of how famous is your website. Someone decided to make a bad joke with a website, for the pure sake of it.
My website is not a product yet, there are no users, subscriptions, or anything, it’s just a landing page with a waitlist.
The first thought when this happens is, how do I fix this as fast as possible?
You have different options.
First of all, I disabled the waitlist endpoint to avoid consuming the whole quota of the external services I use.
Secondly, I needed to add a bot protection. You can do this in different ways. The most popular is to add CloudFlare DDoS protection, which is available for free. I never used it before, and I suppose you need to configure at least the DNS of your website.
But I use Vercel to host my websites, and thankfully they have this option.
I enabled the Attack Challenge Mode, and the problem was mitigated.
But this mode adds an extra page in front of your website, which is fine for a public, non-profit website, but not for your product that needs to be fast and quickly accessible to potential users.
Two seconds of delay can determine if a user will close the browser tab or land on your website.
So, how do you prevent malicious usage without a pre-check stage?
There are two other techniques.
Captcha, and rate limiting.
The captchas are those tools that were particularly used years ago (and they still are) that ask you to solve a puzzle before proceeding with an action. Like, select all the images with a panda inside (I wish it was a panda, but it’s usually a bike, ship, or traffic light).
But the latest version of the most famous captcha service, reCAPTCHA by Google, is smarter. It performs some checks on your browser, and if you look authoritative, there’s no challenge. Exactly, no annoying clicks on blurry images.
If the automatic checks detect something suspicious instead, the challenge is required, and the bot is blocked. Pretty smart 😏
Rate limiting is a technique that counts the number of requests to a specific resource from the same source, in a specific time frame. After X requests, the resource returns an error. For instance, you can allow 10 requests every 60 seconds.
It’s a bit harder to implement because it involves coding or some sort of solution, but modern web services usually provide this functionality out of the box.
I went a bit technical, but this article should give you a brief overview of how to protect your websites and your business.
I hope this helps.
Personal updates
Last week I launched that landing page with a waitlist to validate a product idea (the website that was under attack 👆).
Sometimes I feel the need to write down the changes I apply to my product (copy, new sections, features, and so on) so that I can aggregate it with other metrics like conversions, churn, and so on.
It’ll be very difficult to convert this fuzzy idea into a profitable product, but I still wanted to collect feedback.
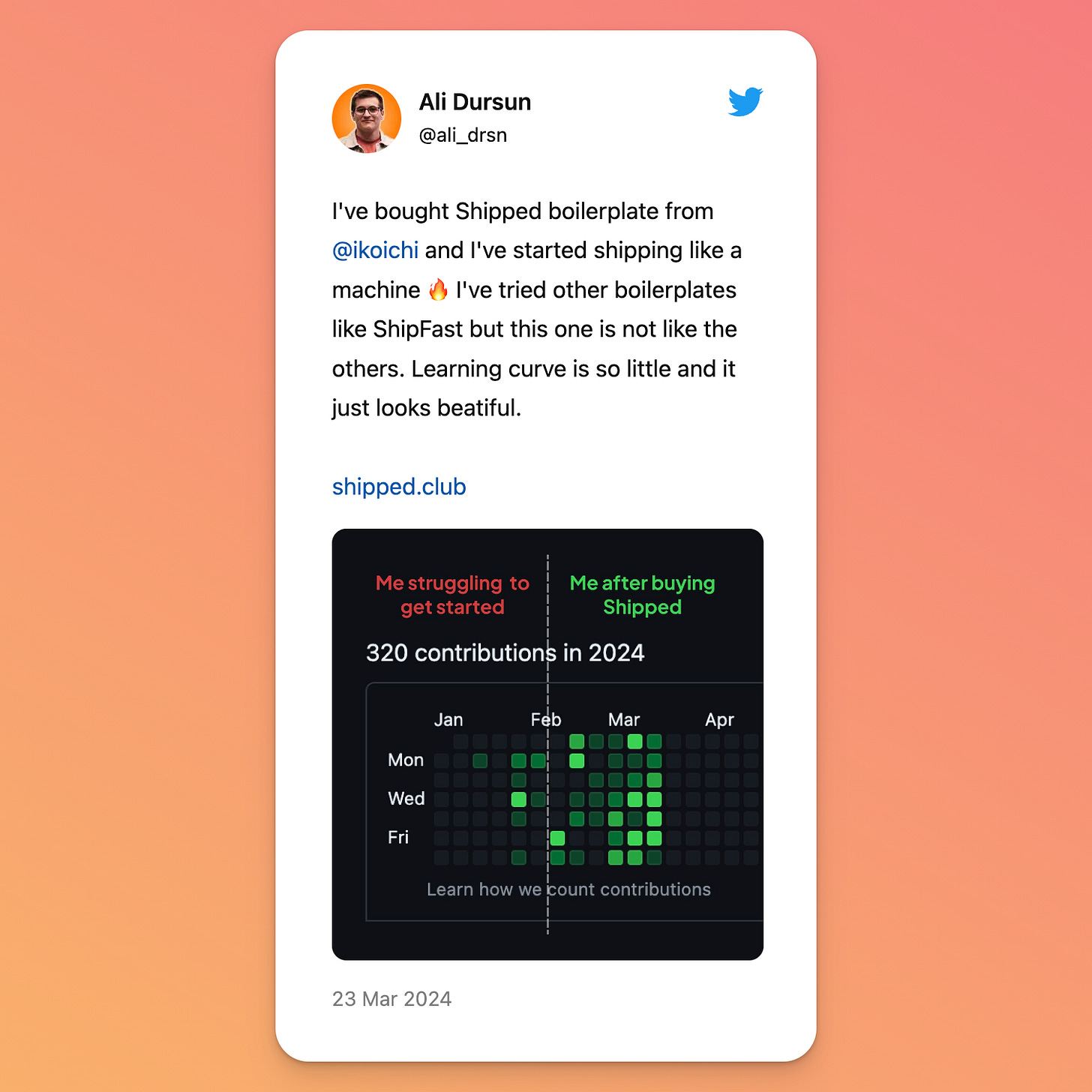
And the risk was very low for me, I spent 2 hours building it, thanks to Shipped.club, so it was a no-brainer decision.
I’ll keep you updated on the results of the validation.
See you next Sunday with more exciting updates!
Luca
Whenever you are ready, I have something to help you.
Shipped.club is the Next.js Startup & Chrome Extension Boilerplate for busy developers, that allows you to build, ship, and make money with your product quickly
152 makers are already shipping like a machine 🔥





Good catch Luca. Quick question, did you get notified when the DDOS attack happened or you randomly checked your vercel dashboard and found out?